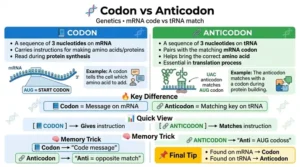
The difference between spoofing and phishing is that spoofing is faking an identity, while phishing is tricking people into sharing sensitive information.
Imagine receiving an email that looks like it’s from your bank that is spoofing. If that email asks you to click a link and enter your password, that becomes phishing.
Understanding the difference between spoofing and phishing helps people stay safe online.
Knowing the difference between spoofing and phishing also improves awareness about cyber threats and how to avoid them in daily digital activities.
🔑 Key Difference Between the Both
The main difference lies in purpose and method.
- Spoofing: Imitates a trusted source.
- Phishing: Steals information through deception.
Examples:
- Spoofing fakes identity.
- It looks real.
Examples:
- Phishing asks for data.
- It tricks users.
🌍 Why Is Their Difference Necessary to Know?
Understanding the difference between spoofing and phishing is important in today’s digital world. Cyber threats are increasing, and many people fall victim due to lack of awareness. Knowing the difference between spoofing and phishing helps individuals recognize suspicious messages, avoid scams, and protect personal and financial information. It also helps organizations improve security practices and reduce risks.
🔊 Pronunciation (US & UK)
| Term | US Pronunciation | UK Pronunciation |
| Spoofing | /ˈspuːfɪŋ/ | /ˈspuːfɪŋ/ |
| Phishing | /ˈfɪʃɪŋ/ | /ˈfɪʃɪŋ/ |
➡️ Now let us explore the detailed difference between spoofing and phishing step by step.
🔐 Difference Between Spoofing and Phishing
1️⃣ Definition
Spoofing is faking identity.
Phishing is stealing information.
Examples:
- Spoofing copies email address.
- It looks real.
Examples:
- Phishing asks for passwords.
- It collects data.
2️⃣ Purpose
Spoofing aims to appear trustworthy.
Phishing aims to get sensitive data.
Examples:
- Spoofing builds trust.
- It deceives.
Examples:
- Phishing steals credentials.
- It exploits trust.
3️⃣ Method
Spoofing uses fake identity.
Phishing uses fake messages and links.
Examples:
- Spoofing changes sender info.
- It imitates.
Examples:
- Phishing uses fake websites.
- It tricks users.
4️⃣ Interaction
Spoofing may not require user action.
Phishing requires user response.
Examples:
- Spoofing shows false identity.
- It may not ask anything.
Examples:
- Phishing asks to click links.
- It needs action.
5️⃣ Target
Spoofing targets systems or users.
Phishing targets individuals.
Examples:
- Spoofing can attack networks.
- It spreads deception.
Examples:
- Phishing targets emails users.
- It focuses on people.
6️⃣ Types
Spoofing includes email, IP, and caller ID spoofing.
Phishing includes email, spear phishing, and smishing.
Examples:
- Spoofing fakes phone numbers.
- It manipulates identity.
Examples:
- Phishing uses SMS scams.
- It tricks victims.
7️⃣ Risk Level
Spoofing creates indirect risk.
Phishing creates direct risk.
Examples:
- Spoofing may lead to fraud.
- It supports attacks.
Examples:
- Phishing directly steals data.
- It causes loss.
8️⃣ Detection
Spoofing is harder to detect.
Phishing can be identified by suspicious requests.
Examples:
- Spoofing looks real.
- It hides well.
Examples:
- Phishing shows warning signs.
- It can be spotted.
9️⃣ Prevention
Spoofing needs technical security.
Phishing needs awareness.
Examples:
- Spoofing requires system protection.
- It uses tools.
Examples:
- Phishing requires caution.
- It needs awareness.
🔟 Example Scenario
Spoofing: Fake email appears from a bank.
Phishing: Email asks for login details.
Examples:
- Spoofing copies branding.
- It looks official.
Examples:
- Phishing asks for password.
- It steals data.
🧠 Nature and Behaviour of Spoofing and Phishing
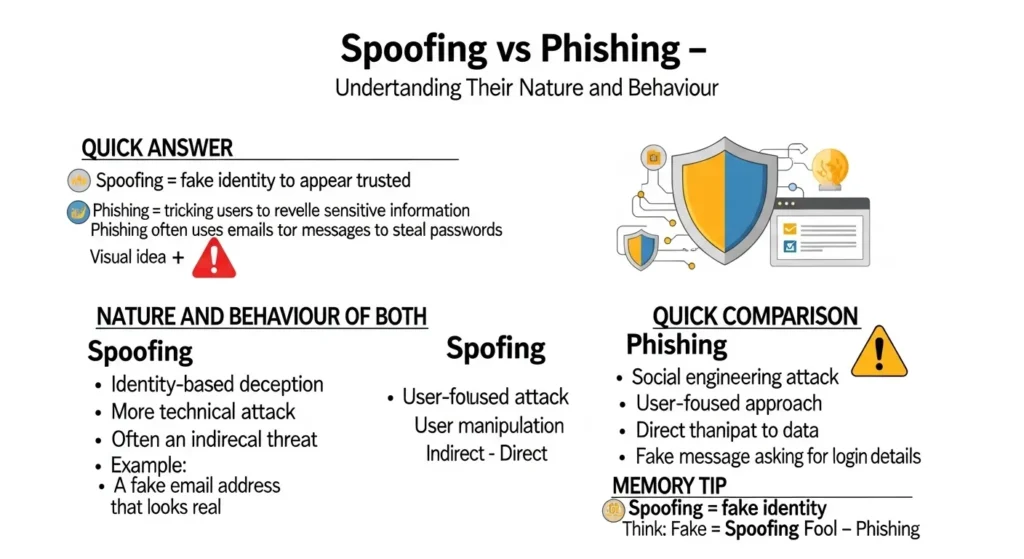
Spoofing
- Identity-based deception
- Technical attack
- Indirect threat
Phishing
- Social engineering attack
- User-focused
- Direct threat
❓ Why People Are Confused About Their Use
People often confuse spoofing and phishing because both involve deception and fake communication. They are often used together in cyber attacks. The confusion becomes clear when understanding that spoofing creates fake identity, while phishing steals information.
📋 Table: Difference and Similarity
| Feature | Spoofing | Phishing |
| Meaning | Fake identity | Data theft |
| Method | Imitation | Deception |
| Target | Systems/users | Individuals |
| Action | Not always needed | Required |
| Risk | Indirect | Direct |
⚖️ Which Is Better in What Situation?
Spoofing
Spoofing is not beneficial; it is used maliciously to impersonate trusted sources. It may be used in testing environments for security purposes.
Phishing
Phishing is also harmful and is used to steal sensitive information. It is never beneficial and should always be avoided.
🎭 Use in Metaphors and Similes
Metaphor example:
- His identity was like spoofing, not real.
Simile example:
- The scam worked like phishing, trapping victims easily.
💬 Connotative Meaning
| Term | Connotation | Example |
| Spoofing | Deception, disguise | The message felt like spoofing. |
| Phishing | Fraud, trickery | The email seemed like phishing. |
🗣️ Expressions
Examples:
- Looks like spoofing
- Feels like phishing
📚 Works in Literature
- “Cybersecurity Essentials” – Charles J. Brooks, 2018
- “The Art of Deception” – Kevin Mitnick, 2002
🎬 Movies Related to Cybersecurity
- “Blackhat” – 2015, USA
- “The Net” – 1995, USA
❔ Frequently Asked Questions
1. What is the main difference between spoofing and phishing?
Spoofing fakes identity, while phishing steals information.
2. Are they related?
Yes, spoofing is often used in phishing attacks.
3. Which is more dangerous?
Phishing is more directly harmful.
4. How to avoid phishing?
Avoid suspicious links and emails.
5. Can spoofing happen without phishing?
Yes, spoofing can occur independently.
🌍 How Both Are Useful for Surroundings
Understanding spoofing and phishing helps improve cybersecurity awareness. It protects individuals and organizations from online threats and fraud.
✍️ Final Words for Both
Spoofing represents disguise and imitation.
Phishing represents trickery and theft.
Both are harmful cyber threats.
🏁 Conclusion
Understanding the difference between spoofing and phishing is essential for online safety. Spoofing involves faking identity, while phishing focuses on stealing sensitive information. Although they are related, their roles are different. Learning these differences helps individuals stay alert and protect themselves in the digital world.
Discover More Articles:

Hi, I’m Nabeel Hassan. I love exploring interesting topics and explaining how different things compare with each other. Through my writing, I aim to provide clear, helpful, and easy to read explanations. I cover subjects related to learning, science, technology and general knowledge.